- Google Cloud Security
- Google Security Operations
- Articles & Announcements
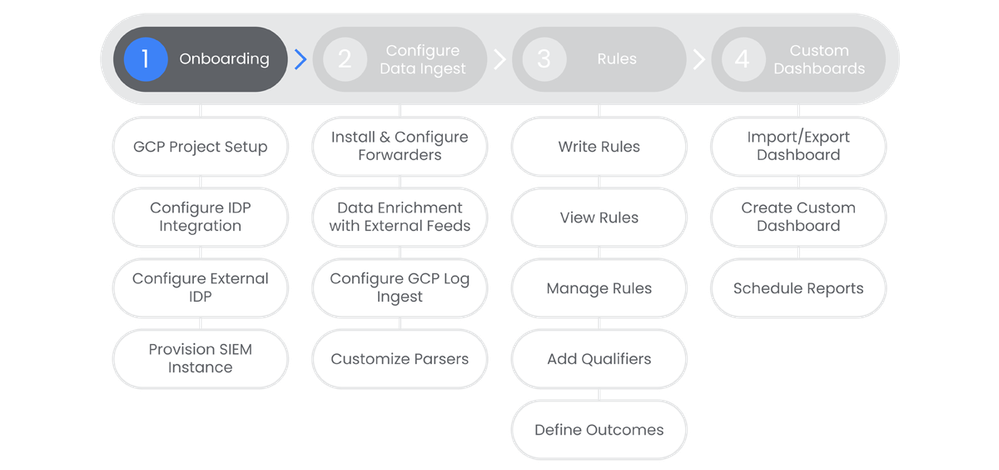
- Onboarding Journey
- Security Operations SIEM: Step 1 - OnBoarding
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Table of Contents
Below you'll find a table of contents for the Onboarding journey.
- Table of Contents
- Prerequisites
- Actions
- GCS Project Setup
- Configure IDP Integration
- Configure External IDP
- Provision SecOps Instance
SecOps Onboarding will provide administrative access to the platform. This is the first requirement in product adoption, and includes integration with your chosen Identity and Access Management (IAM) software to ensure user and role consistency across your portfolio.
Prerequisites
- Entitlement for SecOps SIEM on the account and project
Actions
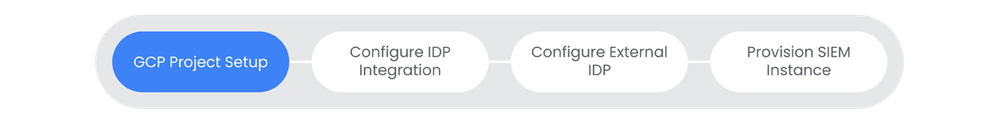
GCS Project Setup
A Google Cloud project is required to use Google Workspace APIs. It is the overarching entity to group services, APIs, billing, collaborators, and managing permissions within your Google Cloud environment.
See the Relevant Links section for more documentation regarding the prerequisites.
- Access to manage Projects inside of your company's Google Workspace. (Presumably the user wouldn't see this step without access to begin with)
Steps
-
In the Google Cloud console, go to Menu > IAM & Admin > Create a Project.
-
In the Project Name field, enter a descriptive name for your project.
-
To edit the Project ID, click Edit. The project ID can't be changed after the project is created, so choose an ID that meets your needs for the lifetime of the project.
-
-
In the Location field, click Browse to display potential locations for your project. Then, click Select.
-
Click Create. The Google Cloud console navigates to the Dashboard page and your project is created within a few minutes.
Relevant Links
- All Steps: https://developers.google.com/workspace/guides/create-projectFIXME: Image
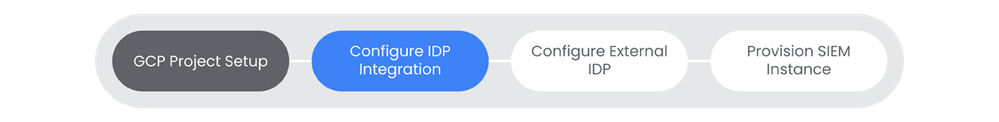
Configure IDP Integration
Identity Platform is a CIAM system that can help you add identity and access management functionality to your Google Cloud projects. Identity Platform is a Google Cloud native IdP.
See the Relevant Links section for more documentation regarding the prerequisites.
- Google Cloud project set up for Chronicle
- Billing Enabled for Google Cloud Project
Steps
-
Select your project from the dropdown at the top of the console.
-
Navigate to the Identity Platform page. | Docs
-
Click Enable Identity Platform.
-
Navigate to the Identity Providers Page > Click Add Provider.
-
In the Select a provider list, select Email/Password.
-
Click the Enabled toggle to on, click Save.
-
Navigate to the Users page. | Docs
-
Click Add User.
-
In the Email field, enter an email and password. Make a note of both of these values because you will need them in a later step.
-
To add the user, click Add. The new user is listed on the Users page.
Relevant Links
- 2: https://console.cloud.google.com/marketplace/details/google-cloud-platform/customer-identity
- 3-6: https://cloud.google.com/identity-platform/docs/sign-in-user-email
- 7: https://console.cloud.google.com/customer-identity/users
- 8-10: https://cloud.google.com/identity-platform/docs/sign-in-user-email
Configure External IDP
If your organization uses an external identity provider (IdP), you will need to configure federation to allow your users, contractors, and partners to authenticate to IAM and Google Console.
See the Relevant Links section for more documentation regarding the prerequisites.
- Administrative access to the Google Cloud Project in which you intend to enable 3rd party IdP.
- Understanding of Google Cloud Workforce Identity Federation.
- Familiarity with Google Cloud Shell.
Steps
-
Define workforce identity pool and provider details. | Docs
-
Define User Attributes and Groups in the IdP. | Docs
-
Create a SAML Application in the IdP and configure it. | Docs
-
Configure workforce identity federation in the Google Cloud. | Docs
-
Create and Configure a workforce identity pool. | Docs
-
Create a workforce identity provider. | Docs
-
Grant roles for SecOps access | Docs
-
Verify or Configure SecOps feature access control. | Docs
-
Modify workforce identity federation configuration. | Docs
Relevant Links
- 1: https://cloud.google.com/chronicle/docs/onboard/configure-authentication#plan_workforce_identity
- 2: https://cloud.google.com/chronicle/docs/onboard/configure-authentication#plan_idp
- 3: https://cloud.google.com/chronicle/docs/onboard/configure-authentication#configure-idp
- 4: https://cloud.google.com/chronicle/docs/onboard/configure-authentication#configure_workforce_identit...
- 5: https://cloud.google.com/chronicle/docs/onboard/configure-authentication#create_and_configure_a_work...
- 6: https://cloud.google.com/chronicle/docs/onboard/configure-authentication#create_a_workforce_identity...
- 7: https://cloud.google.com/chronicle/docs/onboard/configure-authentication#grant_a_role_to_enable_sign...
- 8: https://cloud.google.com/chronicle/docs/onboard/configure-authentication#rbac
- 9: https://cloud.google.com/chronicle/docs/onboard/configure-authentication#modify_the_workforce_identi...
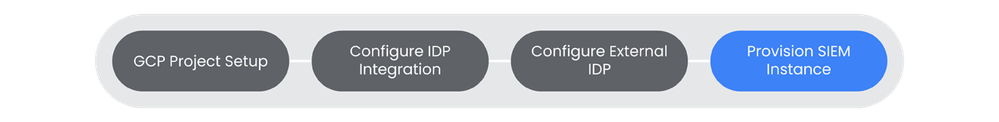
Provision SecOps Instance
In this step we'll provision your SecOps instance using all the pre-work from the previous steps. In order to utilize SecOps, you'll need to have an instance provisioned inside of your Google Cloud Project.
See the Relevant Links section for more documentation regarding the prerequisites.
- Create Google Cloud Project and Enable Chronicle API
- Configure SSO Provider for Chronicle instance
- Confirm User has required permissions
Steps
-
Provide your Customer (CE) with the Project ID you plan to bind to the SecOps Instance. Wait for confirmation email.
-
Select your Google Cloud Project, then navigate to Security > Chronicle SecOps.
-
If you have not enabled the Chronicle API, you will see a Getting Started button, click it.
-
Fill out the Company Information section, click Next.
-
Review the service account information and then click Next.
-
Select the workforce provider created in the previous step of the Chronicle Journey, click Next.
-
Expand the Terms of Service. if you agree to the terms, click Start Setup.
-
Note: It could take up to 15 minutes for the Chronicle instance to be provisioned. You will receive a notification once provisioned successfully.
-
Relevant Links
Next Steps: Security Operations SIEM: Step 2 - Data Ingest

 Twitter
Twitter