- Google Cloud Security
- Security Command Center
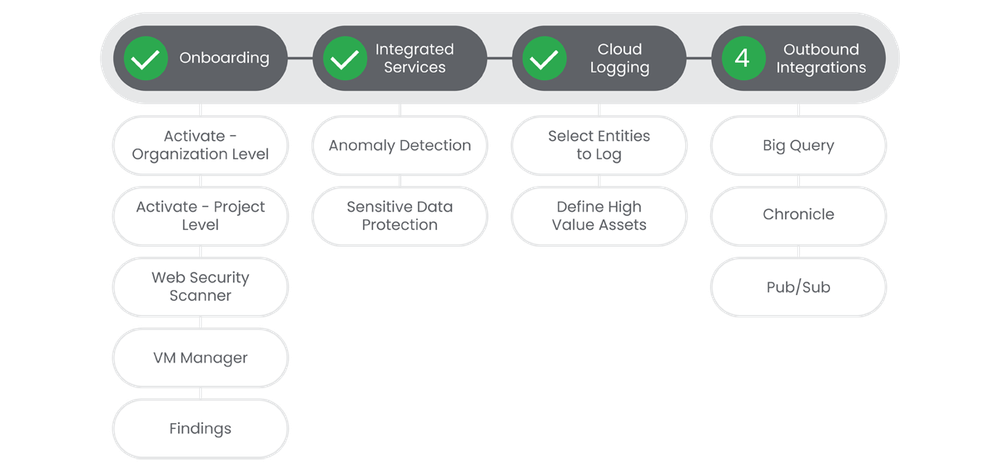
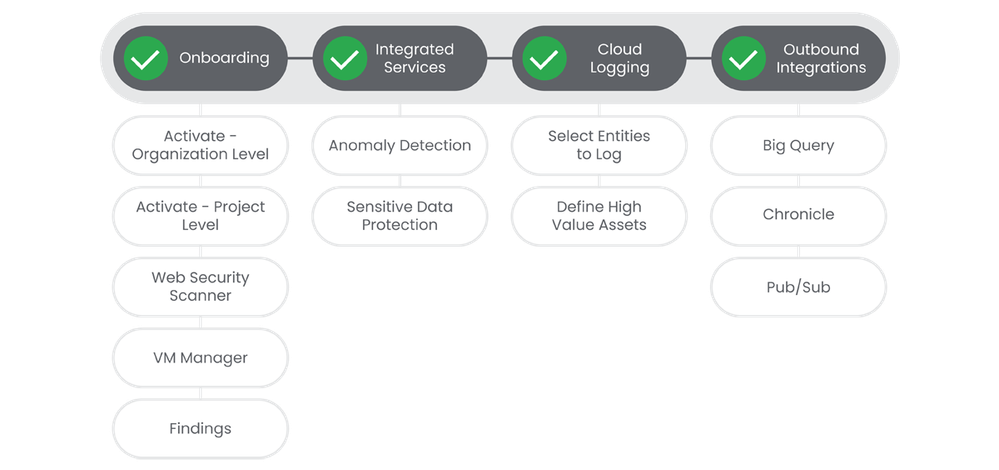
- Onboarding Journey
- Security Command Center Premium: Step 4 - Outbound...
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
Table of Contents
Below you'll find a table of contents for the Outbound Integrations journey.
Security Command Center Premium is powerful in and of itself, but when coupled with Chronicle, BigQuery, or third party tooling, you can achieve a very powerful, holistic, view of your security landscape. Combining all of your security data into a platform like Chronicle SecOps gives you the ability to review, analyze and respond to events in a much faster manner.
Prerequisites
- Security Command Center Premium activated at the Organization or Project level.
- All systems set to UTC time.
Actions
 BigQuery Integration
BigQuery Integration
When you enable exporting of Security Command Center findings to BigQuery, new findings that are written to Security Command Center are exported to a BigQuery table in near real time. You can then integrate the data into existing workflows and create custom analyses. You can enable this feature at the organization, folder, and project levels to export findings based on your requirements.
See the Relevant Links section for more documentation regarding the prerequisites.
- Configure Permissions
- Create BigQuery Dataset
- Enable SCC API
Steps
-
In the Google Cloud Console, select the Project that you enabled the SCC API for.
-
Click Activate cloud shell.
-
To create a new export configuration, run this command:
gcloud scc bqexports create BIG_QUERY_EXPORT --dataset=DATASET_NAME --folder=FOLDER_ID | --organization=ORGANIZATION_ID | --project=PROJECT_ID [--description=DESCRIPTION] [--filter=FILTER]
.
-
Replace
BIG_QUERY_EXPORT
,
DATASET_NAME
,
FOLDER_ID
,
ORGANIZATION_ID
,
PROJECT_ID
,
DESCRIPTION
, and
FILTER
.
-
-
You should see a BigQuery dataset about 15 minutes after running the previous command.
-
Note: If you use VPC Service Controls, please follow the steps in the linked documentation to create an ingress rule for BigQuery.
-
Relevant Links
- Prerequisite: https://cloud.google.com/security-command-center/docs/how-to-analyze-findings-in-big-query#set_up_pe...
- Prerequisite: https://cloud.google.com/bigquery/docs/datasets
- Prerequisite: https://cloud.google.com/security-command-center/docs/how-to-analyze-findings-in-big-query#enable-sc...
- All Steps: https://cloud.google.com/security-command-center/docs/how-to-analyze-findings-in-big-query#setup-new...
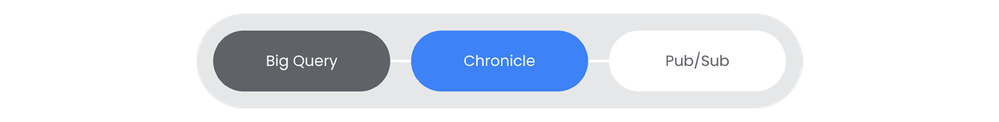
Chronicle Integration
Integrating Security Command Center Premium with your SIEM system provides several significant benefits that enhance your organization's overall security posture: Centralized Security Monitoring, Improved threat detection, Accelerated incident response, and Compliance Reporting.
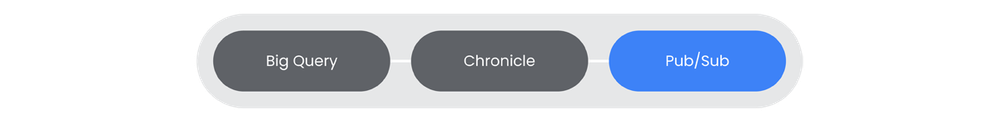
Pub/Sub
Notifications send findings and finding updates to a Pub/Sub topic within minutes. Security Command Center API notifications include all of the finding information that is displayed by Security Command Center in the Google Cloud console. Pub/Sub is useful if your organization or project utilizes a 3rd party SIEM platform.
Prerequisites
See the Relevant Links section for more documentation regarding the prerequisites.
- Apply proper IAM Credentials
- Enable SCC API (If not completed in previous steps)
Steps
-
Create a Pub/Sub topic in the Google Cloud Pub/Sub. | Docs
-
[Optional] If your organization utilizes VPC Service Controls, please complete the steps in the linked docs. | Docs
-
Create a
NotificationConfig
. | Docs
Relevant Links
- All Steps: https://cloud.google.com/security-command-center/docs/how-to-notifications
- Prerequisite: https://cloud.google.com/security-command-center/docs/how-to-notifications#before_you_begin
- Prerequisite: https://cloud.google.com/security-command-center/docs/how-to-notifications#enable-scc-api
- 1: https://cloud.google.com/security-command-center/docs/how-to-notifications#set-up-pubsub-topic
- 2: https://cloud.google.com/security-command-center/docs/how-to-notifications#before_creating_a_notific...
- 3: https://cloud.google.com/security-command-center/docs/how-to-notifications#create-notification-confi...
Complete!
Your journey is now complete.

 Twitter
Twitter