- Google Cloud Security
- Mandiant
- Articles & Information
- Onboarding Journey
- Attack Surface Management: Step 1 - Onboarding
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
- Article History
- Subscribe to RSS Feed
- Mark as New
- Mark as Read
- Bookmark
- Subscribe
- Printer Friendly Page
- Report Inappropriate Content
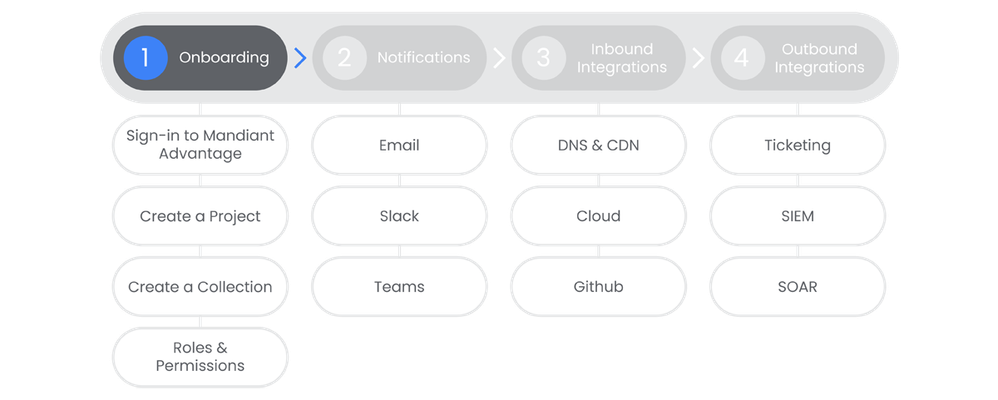
Table of Contents
Below you'll find a table of contents for the onboarding journey.
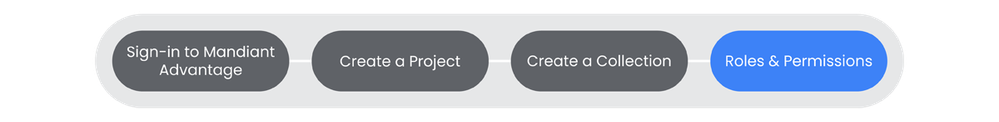
In the onboarding section we will discuss how to gain access to Mandiant Attack Surface Management through Mandiant Advantage, as well as lay the foundational layer of Projects and Collections for your implementation.
Prerequisites
- Have a Mandiant Advantage Account
- Access to Attack Surface Management (ASM) in Mandiant Advantage
- Read and understand ASM Seeds
- Read and understand ASM Technologies
Actions
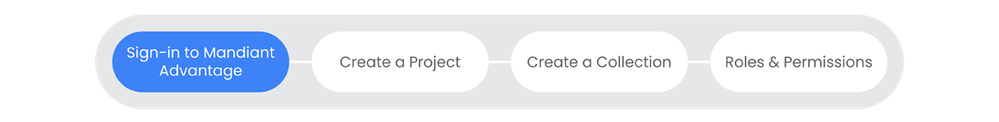
Sign In to Mandiant Advantage
In order to access Mandiant Attack Surface Management (ASM), you need to sign in using your Mandiant Advantage account.
See the Relevant Links section for more documentation regarding the prerequisites.
- Entitlement for Mandiant Attack Surface Management.
Steps
-
Navigate to the Mandiant Advantage Login Page, sign in using your credentials. | Docs
-
Upon login, you will see your profile page. Fill out your profile appropriately.
-
At the top of the profile page, there is an Applications section. In there are links to your deployment of Attack Surface Management, Threat Intelligence, and anything else you are entitled to. Click on Attack Surface Management.
Relevant Links
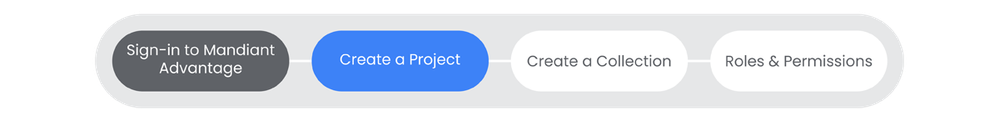
Create a Project
Attack Surface Management (ASM) utilizes projects as a place to manage your Collections and the users who have access to them.
See the Relevant Links section for more documentation regarding the prerequisites.
- Entitlement for Mandiant Attack Surface Management.
Steps
-
Select the organization you would like to create a project in.
-
From the Projects and Settings menu, select My Projects.
-
Click Create New Project.
-
Enter a name for your project, click Create.
Relevant Links
- All Steps: https://docs.mandiant.com/home/asm-projects
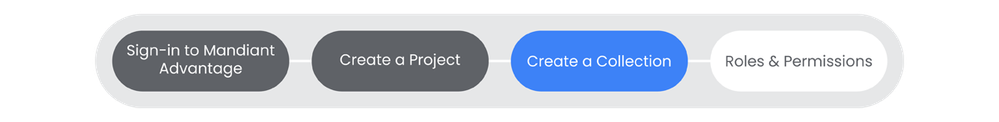
Create a Collection
Collections are lists of assets that are being monitored for protection under Attack Surface Management (ASM). Collections are populated with “Seeds”, entities that are used to uncover other entities that are exposed.
See the Relevant Links section for more documentation regarding the prerequisites.
- Entitlement for Mandiant Attack Surface Management.
- Existing ASM Project
Steps
-
From the ASM console, select Collections > Settings > Create a Collection.
-
Enter a title for your collection and choose a Scan Workflow that best suits your needs, click Next.
-
Enter a Seed and select a Seed Type. Note: You can upload a CSV of seeds following the format referenced in the link.
-
If you would like to add additional seeds, click "+ Add Another."
-
Choose Connect Integration if appropriate in this step. Note: We will be covering integrations in a future section.
-
Choose Create Collection or Create & Run Collection depending on if you would like to run the Collection immediately.
Relevant Links
Roles & Permissions
Roles & Permissions are handled at two levels inside of Attack Surface Management: Project and Collection roles. In order to assume any Collection level roles, a member must have been added to the Project that a Collection lives in.
See the Relevant Links section for more documentation regarding the prerequisites.
- Entitlement for Mandiant Attack Surface Management.
- Existing ASM Project
Steps
-
Click Projects & Settings, choose your Project, click Account Settings.
-
Click Members, then select the appropriate tab: Owners or Members.
-
Owners have the ability to create additional Collections, add Integrations, and Manage Members.
-
-
Click the relevant option: Add Owner or Invite Member.
-
Search for and add each member to the project.
-
Return to the Projects & Settings menu, choose your Project, click Collections, click Settings.
-
Select Settings that are associated with your Collection. Click Groups & Members. Click + Add Groups & Members.
-
For each user, select a Collection Role: Viewer, Analyst, Admin.

 Twitter
Twitter